🧠 AI Quiz
Think you really understand Artificial Intelligence?
Test yourself and see how well you know the world of AI.
Answer AI-related questions, compete with other users, and prove that
you’re among the best when it comes to AI knowledge.
Reach the top of our leaderboard.
Secured AI
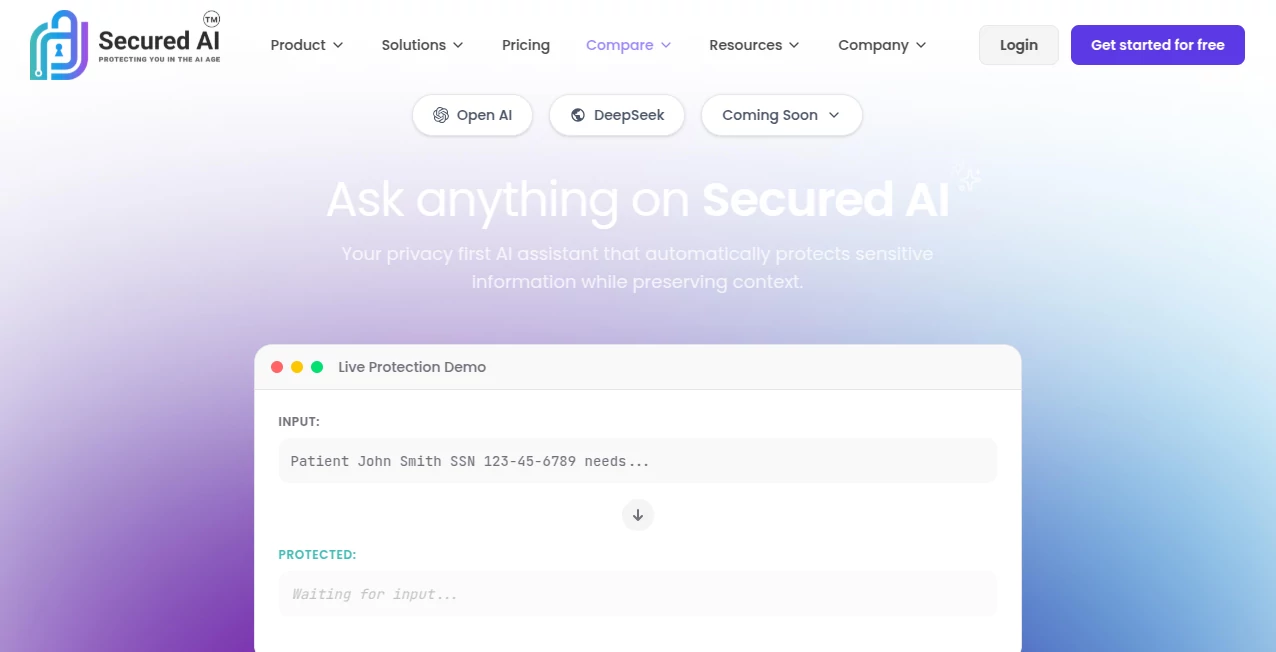
What is Secured AI?
Building with AI is exciting—until you realize how quickly sensitive data, IP, or compliance risks can sneak in. This platform quietly changes that equation. It wraps powerful guardrails around every model, prompt, and output so teams can move fast without waking up to a breach headline. I’ve talked to security leads who used to lose sleep over shadow AI usage; now they sleep better because they can actually see, control, and prove what’s happening inside their organization. It’s not about slowing innovation—it’s about making sure it doesn’t burn the house down.
Introduction
When companies first started adopting generative AI, security was an afterthought. Then came the headlines: leaked prompts, exposed PII, jailbreaks, model inversion attacks. This tool was built exactly for that wake-up moment. It gives security, compliance, and engineering teams visibility and control without killing developer velocity. No more blind spots, no more “we hope nothing bad happens.” Instead, real-time monitoring, automated policy enforcement, detailed audit trails, and risk scoring that actually make sense to both technical and non-technical stakeholders. For organizations that treat AI as mission-critical (and most now do), it’s become the difference between confident scaling and constant firefighting.
Key Features
User Interface
The dashboard strikes a rare balance: clean enough for executives to grasp risk posture in seconds, detailed enough for engineers to drill into specific incidents. Real-time feed shows every prompt and response, flagged risks light up in context, policy violations are color-coded, and drill-downs reveal exactly which model, user, or data triggered the alert. Custom views and role-based access keep noise low—compliance sees high-level trends, SecOps gets raw logs, devs see only what they need to fix. It feels built by people who’ve lived through alert fatigue.
Accuracy & Performance
Detection is sharp—low false positives on prompt injection, data leakage, toxic content, and PII exfiltration. Latency stays negligible even with deep content inspection and multi-model routing. Real-world deployments handle millions of requests daily without slowdowns or dropped events. The risk-scoring engine learns from your organization’s specific patterns over time, so alerts get smarter and more relevant instead of noisier. That tuning is what separates useful security from another tool that gets ignored.
Capabilities
Real-time prompt & response scanning, automated redaction/masking of PII and secrets, policy enforcement (block, warn, log), jailbreak & prompt-injection defense, model-level access controls, audit-ready logs with cryptographic integrity, shadow AI discovery, third-party model risk assessment, and integrations with SIEM, SSO, and major LLM providers. It supports on-prem, VPC, SaaS, and hybrid deployments—flexible enough for regulated industries while staying developer-friendly.
Security & Privacy
Everything is designed with zero-trust in mind. No training on customer data, no shared models, full data residency options, SOC 2 Type II, GDPR, HIPAA, ISO 27001 compliance. Encryption in transit and at rest, fine-grained RBAC, and the ability to air-gap the most sensitive workloads. For enterprises that live under heavy regulation, that level of assurance is non-negotiable—and this platform delivers it without compromise.
Use Cases
A financial services firm routes all internal LLM traffic through the platform, automatically blocking attempts to exfiltrate customer data and logging every interaction for audit. A healthcare provider uses PII redaction to safely allow clinicians to query models without exposing PHI. A large enterprise discovers and brings shadow AI usage under control within weeks of deployment. A defense contractor runs fully air-gapped inference with strict policy enforcement. Wherever sensitive data meets powerful AI, this becomes the control layer that lets innovation continue safely.
Pros and Cons
Pros:
- Best-in-class prompt injection & data leakage prevention with very low false positives.
- Real-time visibility and audit trails that actually satisfy compliance teams.
- Flexible deployment (SaaS, VPC, on-prem, air-gap) without sacrificing features.
- Minimal latency impact—devs barely notice it’s there.
- Risk scoring and policy engine that improve over time with your data.
Cons:
- Setup for on-prem/air-gap deployments takes more time than pure SaaS.
- Advanced behavioral analytics and custom model fine-tuning are higher-tier features.
- Pricing reflects enterprise-grade capability—not ideal for small hobby projects.
Pricing Plans
Pricing is quote-based and scales with usage, deployment type, and feature set. Free trial includes full platform access for 14–30 days (depending on your size). Enterprise plans include dedicated support, custom integrations, and SLAs. Most organizations find the cost modest compared to the potential breach or compliance fine it prevents. It’s positioned as insurance for AI—not an optional nice-to-have.
How to Use SecuredAI
Start with a quick onboarding call or self-serve trial setup. Choose deployment (SaaS, VPC, or on-prem). Configure your models and policies (block PII, require approval for certain prompts, etc.). Route traffic through the proxy/API gateway. Watch the dashboard populate with real-time activity, flagged risks, and compliance reports. Adjust policies based on what you see—most teams lock down high-risk patterns within the first week. Once configured, it runs silently in the background, only surfacing when something needs attention.
Comparison with Similar Tools
Some competitors focus heavily on prompt filtering but lack deep data-loss prevention or audit integrity. Others are strong on compliance reporting but add noticeable latency. This platform balances both—strong detection, minimal performance impact, flexible deployment, and audit-grade logging. It’s less about being the cheapest and more about being the most trustworthy when regulators or auditors come knocking.
Conclusion
AI is moving too fast to secure it with yesterday’s tools. This platform gives organizations the visibility, control, and peace of mind to adopt powerful models without gambling on security. It turns “we think we’re safe” into “we can prove we’re safe”—and in boardrooms and audit meetings, that proof is priceless. For teams serious about scaling AI responsibly, it’s not just helpful; it’s becoming essential.
Frequently Asked Questions (FAQ)
How much latency does it add?
Typically <50ms for most requests—often imperceptible to end users.
Does it work with on-prem models?
Yes—air-gapped and VPC deployments are fully supported.
Can I customize policies per model or team?
Yes—granular controls down to the user, group, or model level.
Is my data used to train anything?
No—zero customer data is used for training or shared externally.
What compliance standards are covered?
SOC 2 Type II, GDPR, HIPAA, ISO 27001, and more—audit reports available.
These classifications represent its core capabilities and areas of application. For related tools, explore the linked categories above.
Secured AI details
This tool is no longer available on submitaitools.org; find alternatives on Alternative to Secured AI.
Pricing
- Free
Apps
- Web Tools