🧠 AI Quiz
Think you really understand Artificial Intelligence?
Test yourself and see how well you know the world of AI.
Answer AI-related questions, compete with other users, and prove that
you’re among the best when it comes to AI knowledge.
Reach the top of our leaderboard.
VoiceMOAT
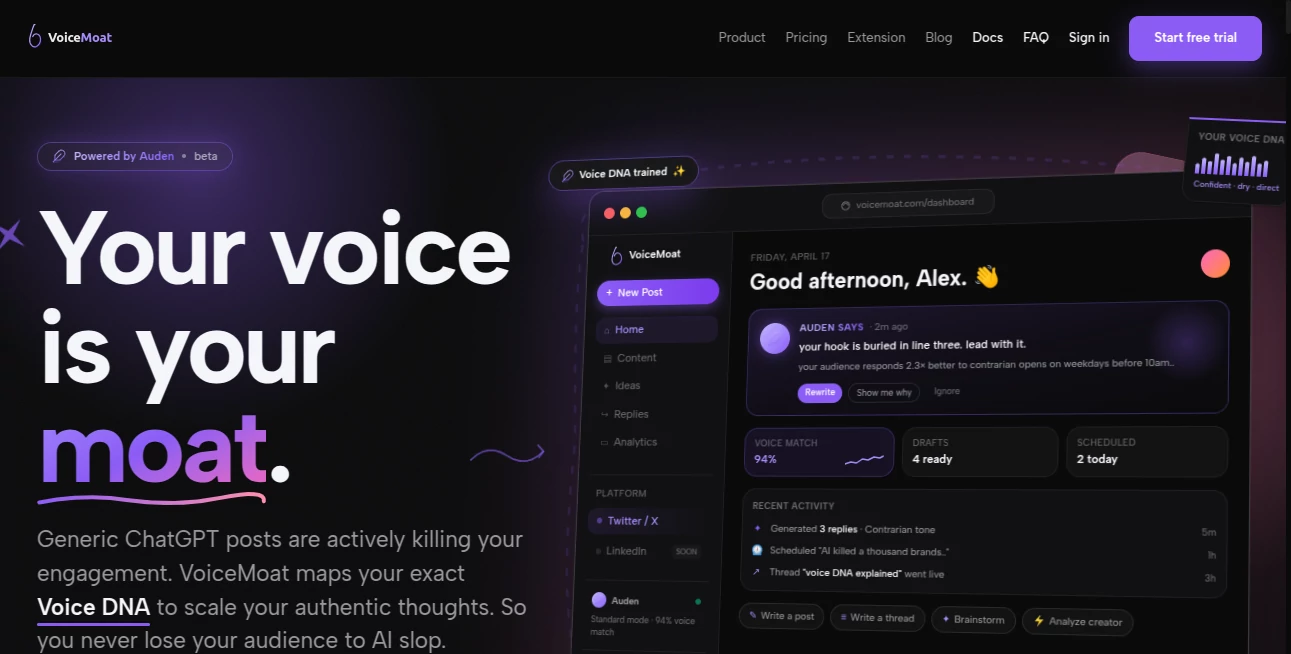
What is VoiceMOAT?
Have you ever had that uncomfortable feeling that maybe, just maybe, someone is listening a little too closely? Not just the person you're talking to, but something else. Something automated. Something that doesn't get tired, doesn't blink, and is getting smarter by the day.
The truth is, our voices have become a form of digital ID. Every time you speak into a device, you're not just sharing words. You're sharing your emotional state, your age range, your speaking patterns, and even clues about your environment. And in the wrong hands, that's pure gold for fraudsters. That is exactly why this tool arrived at the perfect moment. It stops treating voice security like a simple lock and starts treating it like a living, breathing security system that actually understands what a real human sounds like.
Key Features
What makes this platform genuinely different isn't just one clever trick. It is a whole toolbox designed to separate your genuine voice from every imitation, recording, or synthetic clone out there. Let me walk you through what actually happens under the hood.
User Interface
Nobody wants to wrestle with a confusing dashboard when they are worried about security. The whole experience here feels refreshingly straightforward. You are not bombarded with cryptic settings or technical jargon. Instead, you get a clean overview that shows you exactly what is being protected at any given moment.
For businesses integrating this into their contact centers, the interface plugs right into existing workflows without forcing agents to learn a whole new language. It sits quietly in the background, doing its job, and only pops up when something genuinely suspicious happens. That is exactly how good security should feel – invisible until it is needed.
Accuracy & Performance
Here is where things get genuinely impressive. The platform doesn't just check if a voice sounds familiar. It runs it through multiple layers of checks in real time. We are talking about analyzing over a hundred different acoustic and behavioral parameters during a single conversation .
The system is built to catch the really sneaky stuff too. Research in this space shows that modern detection tools can identify synthetic voices generated by systems they have never even encountered before, with detection rates reaching into the high nineties for known deepfake engines . That means when a new AI voice cloning tool drops next week, this system won't be caught sleeping. It adapts. It learns. And it keeps your conversations safe.
Capabilities
Let me paint you a picture. Imagine someone has managed to grab a few seconds of your voice from a social media video. They feed it into a voice cloning tool, and now they have a synthetic version of you. They call your bank. What happens?
With traditional systems, they might actually get through. But this platform looks for the tiny tells that no machine can fully hide. It picks up on unnatural pauses. It detects the absence of natural breath sounds. It notices when voice patterns are just too perfect, because real humans are wonderfully imperfect .
The system also performs continuous authentication. It does not just check you once at the door. It keeps verifying throughout the entire conversation. If someone passes the phone to a different person mid-call, the system flags that instantly. If a deepfake tries to take over after the initial greeting, it gets caught.
Security & Privacy
This is the part where most people's eyes glaze over, but stick with me because this matters. The platform does not store your actual voice recordings like some vulnerable file sitting on a server waiting to be stolen. Instead, it creates a mathematical representation of your voice characteristics, called an encrypted embedding .
Even if a hacker somehow grabbed that data, they could not reverse it back into your actual voice. It is useless to them. This zero-knowledge approach means your voice stays yours. The system also includes tamper detection, so you know immediately if anyone has tried to mess with the stored data.
Use Cases
So who actually needs this? Pretty much anyone who uses their voice to access something valuable.
Contact centers in banking and finance are the obvious heavy users. When someone calls to check their balance or transfer money, the system silently authenticates them in the background. No more security questions that take two minutes. No more frustration for the customer. Just seamless, secure access .
But it goes beyond that. Healthcare providers use it to protect patient calls that contain sensitive medical information. Government agencies rely on it for secure communications. Even everyday people who want to protect their smart home devices from being tricked by recorded commands find real value here.
And here is a scenario you might not have considered: virtual meetings. Imagine you are on an important video call discussing a potential acquisition. The platform can verify in real time that the person speaking is actually who they claim to be, not a deepfake sitting in a bedroom somewhere .
Pros and Cons
Pros:
The multi-layered detection is genuinely best-in-class. It catches things that human ears simply cannot hear, like the subtle frequency distortions left behind by AI voice generators. The continuous authentication during calls means a single point of failure never compromises your security.
The system also handles real-world messiness well. Got a cold? Your voice sounds different. The platform recognizes illness patterns and can step up verification through other methods instead of just locking you out . That is thoughtful design.
Cons:
Nothing is perfect. The initial enrollment requires you to provide multiple voice samples to build an accurate profile. For some users, that might feel like a small hassle. Additionally, while the false positive rate is very low (well under one percent in most implementations), no security system can promise absolute perfection .
Some very specific accents or speech impediments might require additional calibration, though the system is generally quite flexible across different languages and speaking styles.
Pricing Plans
The platform operates on a tiered model designed to fit different needs. For individual users or small teams, there is a freemium option that gives you basic deepfake detection and voice authentication for a limited number of calls per month. Enough to get a real feel for the technology without spending a dime.
The professional tier unlocks higher usage limits, faster processing, and access to the continuous authentication features. Enterprise customers get the full suite: multi-layered detection, dedicated support, deployment options for contact centers, and integration with existing security infrastructure like SIEM systems.
For the most accurate and up-to-date pricing, you should visit the website directly. They frequently add new features and adjust plans based on what customers actually need.
How to Use VoiceMoat
Getting started takes about ten minutes. First, create your account using a valid email address. The platform will walk you through the enrollment process, asking you to record several short phrases in a quiet environment. Do not worry about sounding perfect. Natural, everyday speech is actually better for creating an accurate voiceprint.
Once your profile is created, you can start protecting your calls immediately. For individual use, there is a browser extension that integrates with common video conferencing platforms. For businesses, the API allows seamless integration into existing phone systems and contact center software.
The dashboard gives you access to logs showing every authentication attempt. You can see where attempts came from, whether they succeeded or failed, and if any suspicious activity was detected. This audit trail is invaluable for security teams monitoring for potential threats.
Comparison with Similar Tools
You might be wondering how this stacks up against other options out there. Several players in the voice security space offer decent solutions. Pindrop, for example, has strong deepfake detection with their Pulse product, achieving impressive detection rates in controlled environments . Omilia offers solid multi-factor approaches for contact centers .
Where this platform pulls ahead is in its balanced approach. Other tools often excel at one thing but fall short elsewhere. Some focus heavily on deepfake detection but offer a clunky user experience. Others prioritize speed but sacrifice depth of analysis.
This solution combines genuinely effective liveness detection with continuous authentication and a user-friendly interface. It also handles edge cases better than most, dealing gracefully with voice changes due to illness or aging. The zero-trust architecture means every interaction is treated with appropriate scrutiny, not just the first handshake .
The open-source community has produced some interesting projects like VoiceGuard and Sivaji Security System, but these require significant technical expertise to deploy and maintain . This platform offers enterprise-grade security without needing a team of engineers to babysit it.
Conclusion
Look, the world of AI voice manipulation is not coming. It is already here. Deepfakes are getting better every single week. The tools to clone a voice are available to anyone with an internet connection and a few dollars .
Waiting until after an attack happens to think about voice security is like buying a fire extinguisher while your kitchen is burning. This platform gives you peace of mind. It lets you have conversations, run your business, and connect with people without that nagging worry in the back of your mind.
The technology works. It is proven in real-world deployments across banks, healthcare providers, and government agencies. And it manages to do all of this without making legitimate users jump through endless hoops. That is the holy grail of security: strong enough to stop the bad guys, smooth enough that the good guys barely notice it is there.
You do not need to be a security expert to use it. You just need to care about protecting your conversations. And if you have made it this far, it is pretty clear that you do.
Frequently Asked Questions (FAQ)
Can this system be fooled by a recording of my voice?
No. The liveness detection specifically looks for signs of recorded audio, such as inconsistencies in background noise, lack of natural breath patterns, and the absence of the subtle acoustic variations that happen when a real human speaks. A recording will be flagged almost instantly .
What happens if I lose my voice due to illness?
The system is designed to recognize when a voice sounds different due to temporary factors like illness. In these cases, it can fall back to step-up authentication methods, such as sending a one-time code to your phone, rather than simply denying you access .
Does the platform work with any language or accent?
Yes. The underlying models are trained on diverse voice data from multiple languages and dialects. While performance is strongest for major languages, the system handles accents and regional variations far better than older generation tools that expected everyone to sound like a newscaster.
Is my voice data stored securely?
Absolutely. The platform uses encrypted voiceprints, not raw recordings. Even if someone accessed the stored data, they could not reconstruct your actual voice. All data is protected with military-grade encryption both at rest and in transit.
AI Voice Assistants , AI Speech Recognition , AI Voice & Audio Editing .
These classifications represent its core capabilities and areas of application. For related tools, explore the linked categories above.
VoiceMOAT details
Pricing
- Free
Apps
- Web Tools
Categories
VoiceMOAT Alternatives Product
TurboScribe
Krisp
Goose Pod
AssiPilot
Flow Song
LPM 1.0
Models by Ha…
Chatterbox T…
Gpt Realtime